Services
Turn Detection Into Action
Guard Hawk extends the Command Platform with monitoring, detection tuning, and response support - ensuring threats are identified, validated, and acted on in real time.
Service Model
Choose How You Operate
Platform-Enabled
Self-Directed — Use Guard Hawk to monitor and manage your own environment.
Platform access
Detection visibility
Alerting
Internal team ownership
Guard Hawk-Assisted
We work alongside your team to tune detection, validate alerts, and improve coverage.
Detection optimization
Alert validation
Ongoing guidance
Fully Managed
Guard Hawk handles monitoring and response for you.
Continuous monitoring
Incident triage
Alert escalation
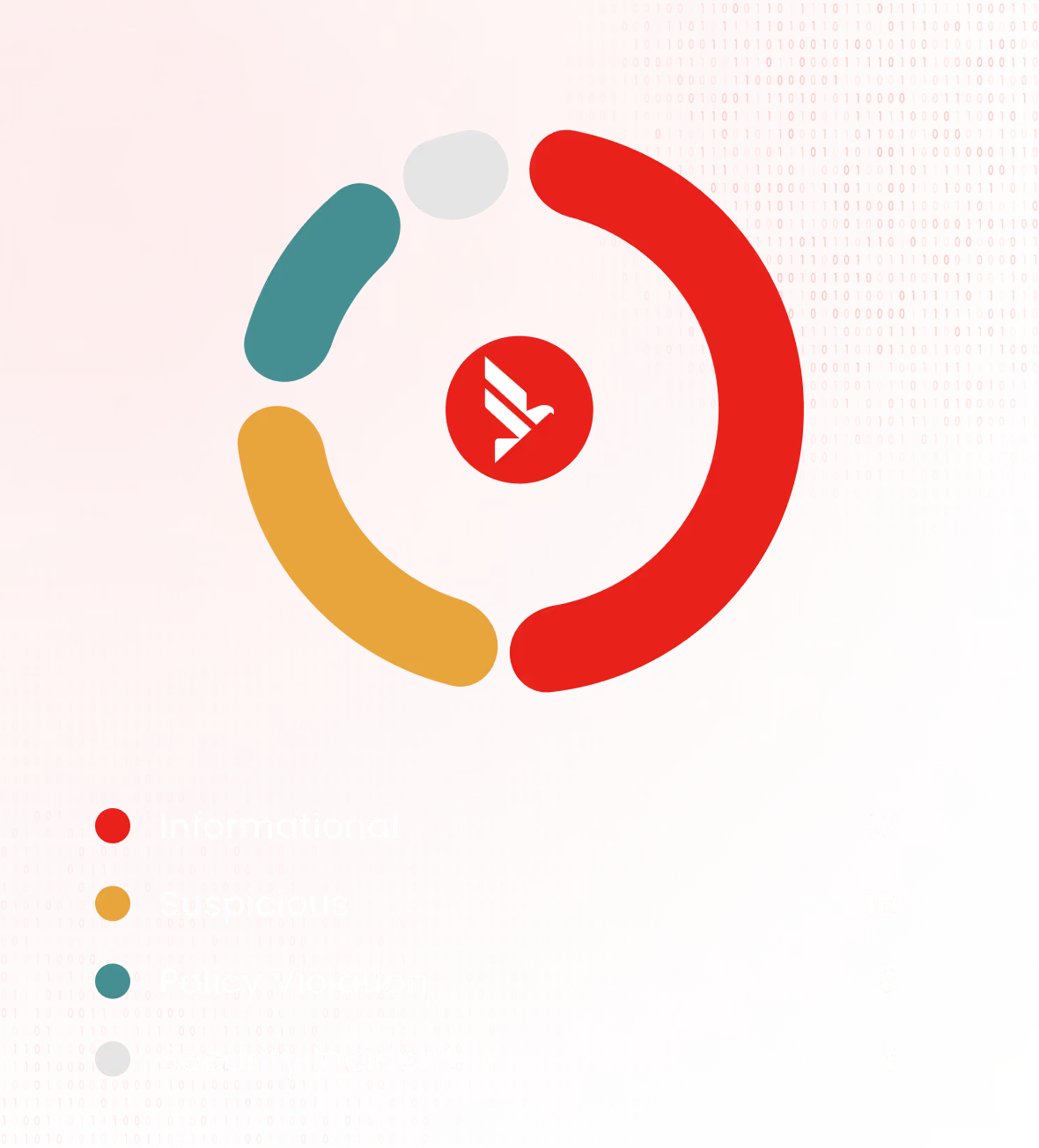
Core Service Categories
What We Deliver
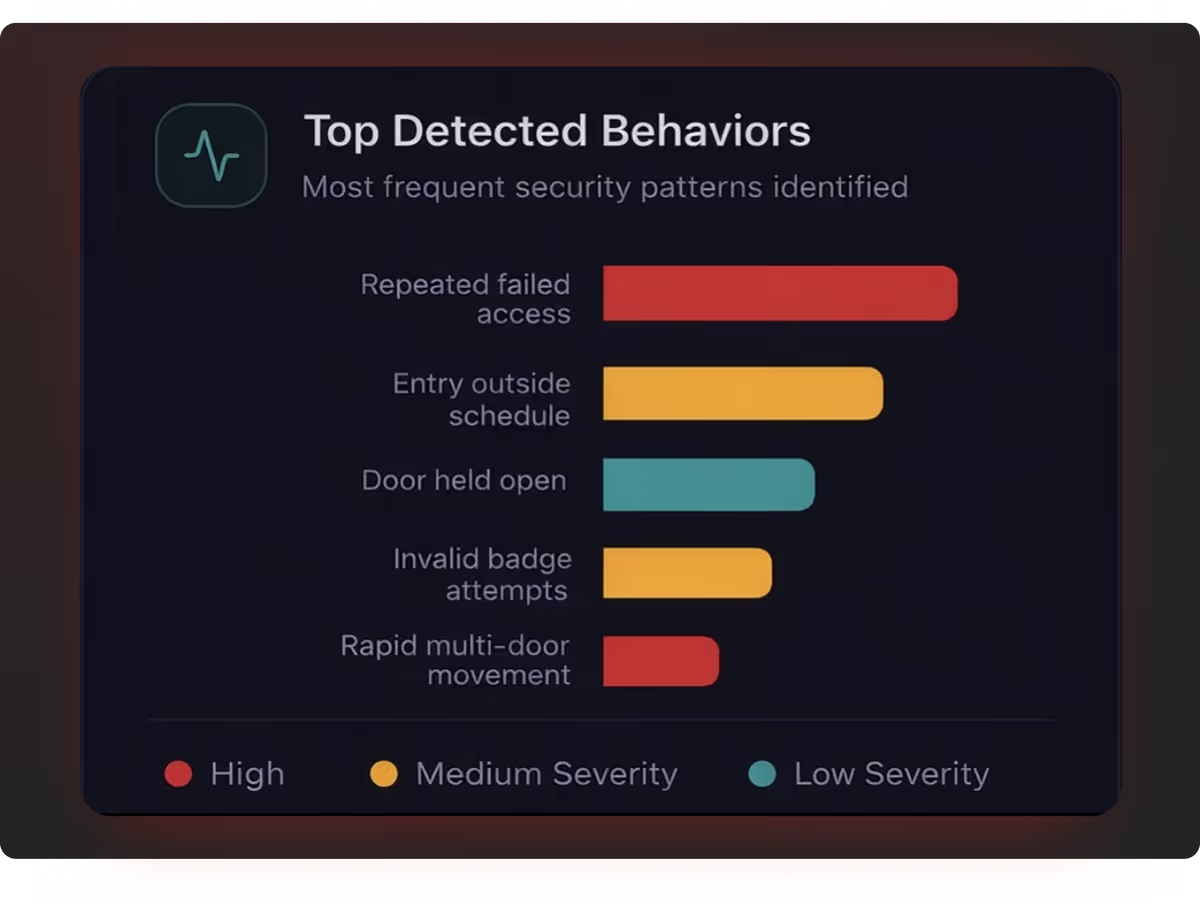
Threat Detection & Correlation
Detection-focused monitoring across systems
Threat detection
Event correlation
Alerting
Investigation support
System Health & Integrity Monitoring
Operational + system integrity monitoring
System uptime
Configuration drift
Service disruptions
Performance anomalies
Monitoring Approach
How We Monitor
Guard Hawk unifies telemetry from physical security systems, identity platforms, and supporting infrastructure into a centralized detection environment.
Ingest data across systems and environments
Correlate signals across physical and digital layers
Continuously monitor for threats and anomalies
Deliver context-aware alerts, not noise
Service Tiers
Choose Your Level of Coverage
Foundation Monitoring

Visibility

Basic alerting

Baseline logging
Advanced Monitoring

Detection tuning

Correlation

Deeper analysis
Managed Monitoring

Full coverage

Continuous oversight

Incident support
Where Services Apply
Built for Real Environments
Commercial Facilities
Office buildings, campuses, retail
Logistics & Warehouses
Distributed access control monitoring
Industrial Sites
OT-adjacent, segmented environments
Corporate Infrastructure
Multi-site enterprise environments
Why Guard Hawk
What Sets Us Apart
Platform-First Approach
Vendor-Neutral
Detection-Driven
Real-World Systems Focus
Get Started
