Product - Edge Deployment
Guard Hawk Talon
Guard Hawk Talon is an on-site telemetry collector that securely brings physical security system data into the Command Platform - without changing your network.

What It Is
Secure Telemetry at the Edge
Guard Hawk Talon is a lightweight on-site collection layer that enables secure, controlled telemetry ingestion from infrastructure systems - designed to operate within existing network boundaries without disrupting critical environments.
Deployment
Deployed On-Site
Detect unauthorized access attempts, role changes, and system failures — correlating events across doors, controllers, and identity systems.
Collection
Collects Telemetry
Connects within approved VLANs. Collects syslog, SNMP, and other telemetry from physical security systems.

Security
Stays Within Boundaries
Works within client network boundaries — no external agents, no proprietary lock-in, no infrastructure changes required.
Forwarding
Deployed on-Site → Sends to Command Platform
Telemetry is securely forwarded to the Guard Hawk Command Platform for detection, correlation, and alerting.
Why It Matters
Built for Real Environments
ONBOARDING FRICTION
Reduces Deployment Complexity
Deploy quickly without disrupting existing systems or requiring complex network reconfigurations.
VISIBILITY
Expands Coverage
Reach systems that traditional deployment models can't access - segmented OT/IT environments included.
NETWORK COMPLIANCE
Works Within Boundaries
Works within approved client network segments, respecting VLAN architecture and existing security policy.
AGENT-LESS
Supports Agent-Less Environments
Ideal for environments where installing agents is not feasible or permitted due to policy or architecture constraints.
Deployment
How its works
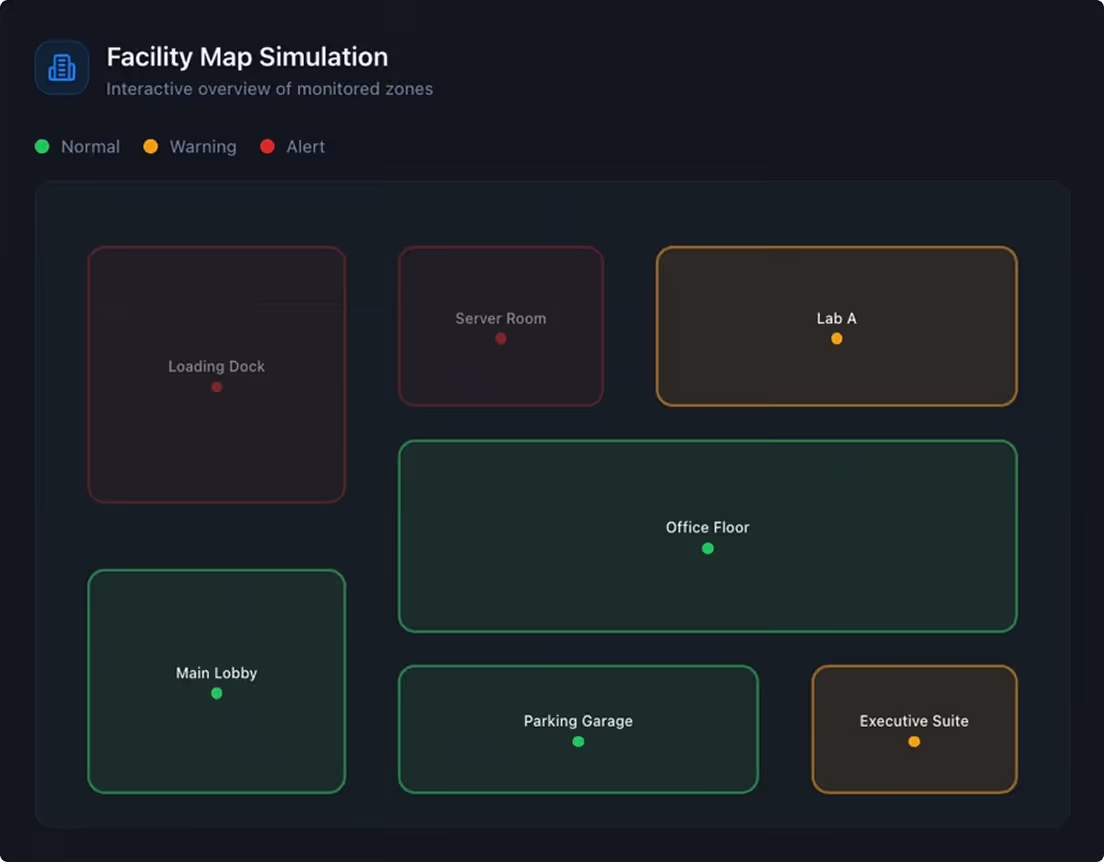
A unified detection platform connecting physical security systems and IT infrastructure.
01
On-Site Deployment
Talon is deployed physically within the customer environment.
02
Network Segmentation
Connects within approved network segments — no boundary crossing.
03
Telemetry Collection
Collects via syslog, SNMP, and other supported protocols.
04
Secure Forwarding
Telemetry is securely forwarded to the Guard Hawk Command Platform for detection, correlation, and alerting.
Use Cases
Deployed Across Complex
Environments
Warehouses
Distributed access control across large facilities
Physical Security Networks
Segmented VLAN environments
Industrial Facilities
OT-adjacent, segmented environments
Multi-Site Environments
Centralized visibility across many locations
Part of the Ecosystem
How Guard Hawk Fits into the Guard Hawk Platform
Talon extends the Command Platform - enabling broader visibility across environments where traditional deployment models may not apply.
Together, Talon and the Command Platform provide end-to-end detection from the edge to the core - giving your security team complete situational awareness.
Together, Talon and the Command Platform provide end-to-end detection from the edge to the core - giving your security team complete situational awareness.
Differentiation
Why Talon Is Different
No agents required
Deploy without installing software across endpoints or systems.
Built for physical security systems
Purpose-built for access control, surveillance, and infrastructure.
Designed for segmented environments
Operates within restricted and isolated network zones.
No network reconfiguration
Works within existing infrastructure without disruption.
Extends beyond traditional IT visibility
Brings physical and cyber systems into one detection layer.
Get Started
