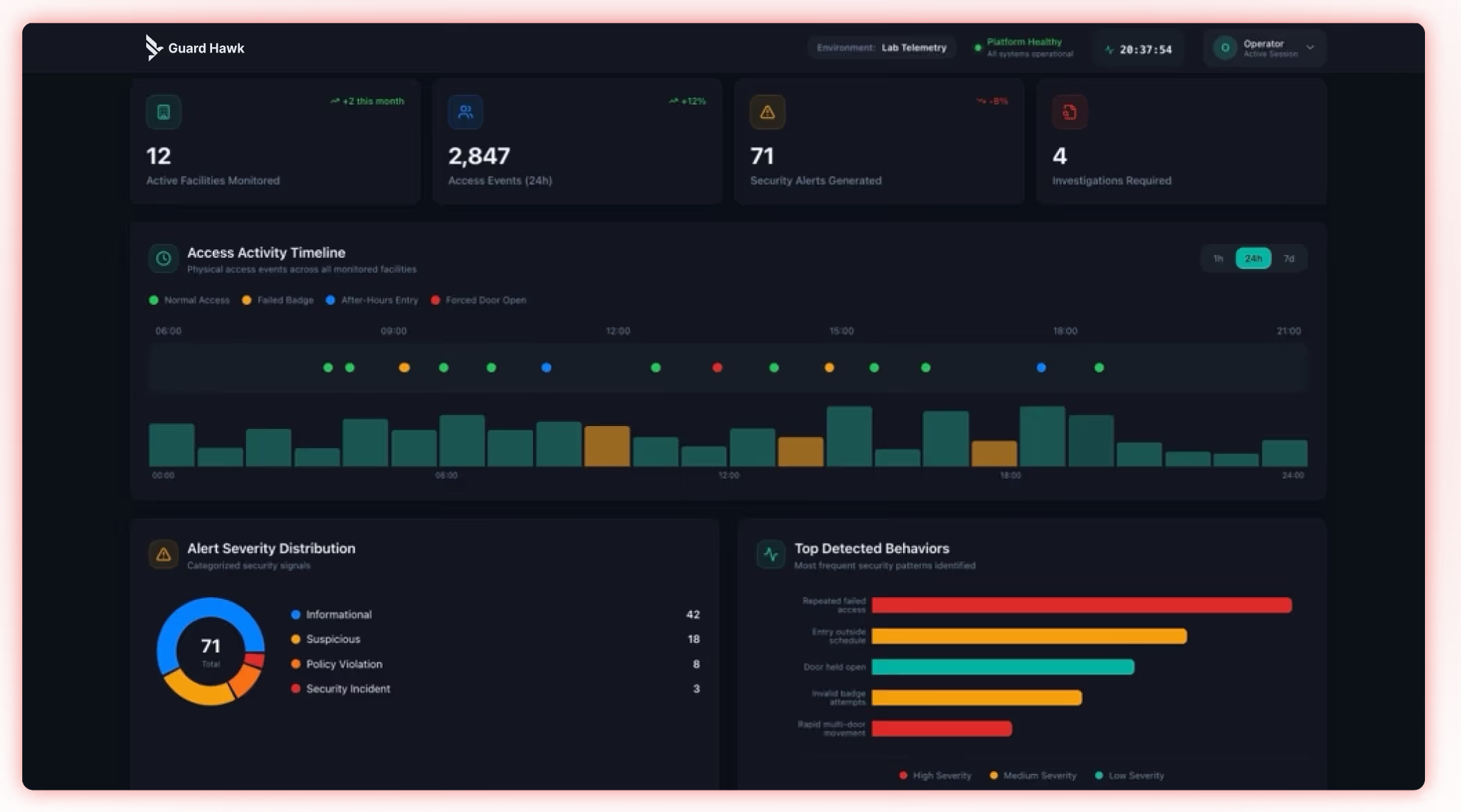
The Guard Hawk Command Platform
Uncover Threats Your Security Stack Is Missing
Most security tools monitor systems in isolation. Guard Hawk connects physical access, identity, and infrastructure signals to detect threats others miss - before they escalate.
What It Does
Built to Detect What Others Miss
Most monitoring tools stop at logs. Guard Hawk turns telemetry into detection.
Guard Hawk connects telemetry from physical security systems and supporting infrastructure into a centralized detection environment.
Guard Hawk connects telemetry from physical security systems and supporting infrastructure into a centralized detection environment.
Collect telemetry across systems and environments
Real-time threat detection
Cross-system event correlation
Collect telemetry across systems and environments
Architecture
How It Works
01
Data Collection
Agents - endpoints, servers
Syslog - firewalls, appliances
APIs - platform integrations
Future: Talon edge collector
02
Analyze
Rule-based + custom detection logic
Threat + anomaly detection
Identity-based monitoring
03
Detect & Respond
Real-time alerts
Dashboards & event correlation
Investigation workflows
Detection Intelligence
Detection Built for Real-World Systems
Identity Misuse Detection
HID Integration
Detect correlated anomalies between badge activity, identity systems, and network behavior — not isolated access events.
Access Anomalies
Genetec / LenelS2
Real-time detection of unauthorized access attempts, after-hours entries, and system configuration changes.
System Misuse / Tampering
Infrastructure Anomalies
Identify controller communication failures, configuration drift, and behavioral signals indicating system interference.
Operational Anomalies
System Behaviour Monitoring
Surface abnormal system behaviour, performance deviations, and operational patterns that indicate risk before incidents occur.
Supported Environments
Designed for Vendor-
Neutral Environments
Access Control Systems
Genetec, LenelS2, HID
Video Surveillance
NVRs / DVRs / IP Cameras
Network Infrastructure
Firewalls, switches, appliances
Identity
Systems
Systems
HID, Active Directory
Deployment
Flexible Deployment Options
Current
Agent-Based
Deployed on endpoints and servers for full telemetry collection across your environment.

Full endpoint visibility

Deep log collection

Identity-level monitoring
Coming via Talon
Agent-Less
Via the Talon edge collector — visibility without touching endpoints or requiring agents.

No endpoint installation

VLAN-aware collection

Syslog + SNMP ingestion
Flexible
Hybrid
Mix agents and Talon across your environment for complete coverage in complex deployments.

Mixed environment support

Unified detection layer

Centralized visibility
Platform Outcomes
What You Gain
Early Threat Detection
Catch threats before they become incidents
System-Wide Visibility
One view across all physical and IT systems
Reduced Blind Spots
Close the gap between cyber and physical
Faster Response
Act with context, not just raw alerts
Detection Validation
Detection Validation in Practice
See how Guard Hawk identifies, validates, and responds to real-world threats across physical and digital environments.
CASE STUDY
Logistics & Warehouse Environment
Multi-site infrastructure monitoring across access control and endpoints
Environment remained stable with key risks identified and addressed proactively.
148
Alerts Analyzed
6
High Severity
2
Validated Events
0
Breaches
After-Hours Access Anomaly
Door forced open at rear loading dock outside operating hours.
- After-hours activity detected
- Physical entry point exposed
- Door unsecured for ~4 minutes
Action: Alert escalated, camera verification advised
Outcome: Potential security gap identified
Credential Misuse Risk
Multiple failed login attempts on
shared workstation.
shared workstation.
- Off-hours activity
- Shared credentials risk
- Threshold exceeded
Action: Password reset + policy review
Outcome: Resolved successfully
After-Hours Access Anomaly
- After-hours activity is a major risk vector
- Shared credentials increase exposure
- Detection rules are working effectively
Credential Misuse Risk
- Enforce stricter after-hours access
- Remove shared accounts
- Integrate video validation
- Expand network visibility
Get Started
