Cross-System Threat Detection
Uncover Threats Your
Security Stack Is Missing
Most security tools monitor systems in isolation. Guard Hawk connects physical access, identity, and infrastructure signals to detect threats others miss - before they escalate.
The Gap
The Security Blind Spot Most Organizations Miss
Physical security systems and IT systems operate in silos
Threat signals exist across both environments
Disconnected tools hide critical warning signs
Most platforms monitor one side - not both
Guard Hawk connects these signals into a single, real-time detection layer.
Detection Intelligence
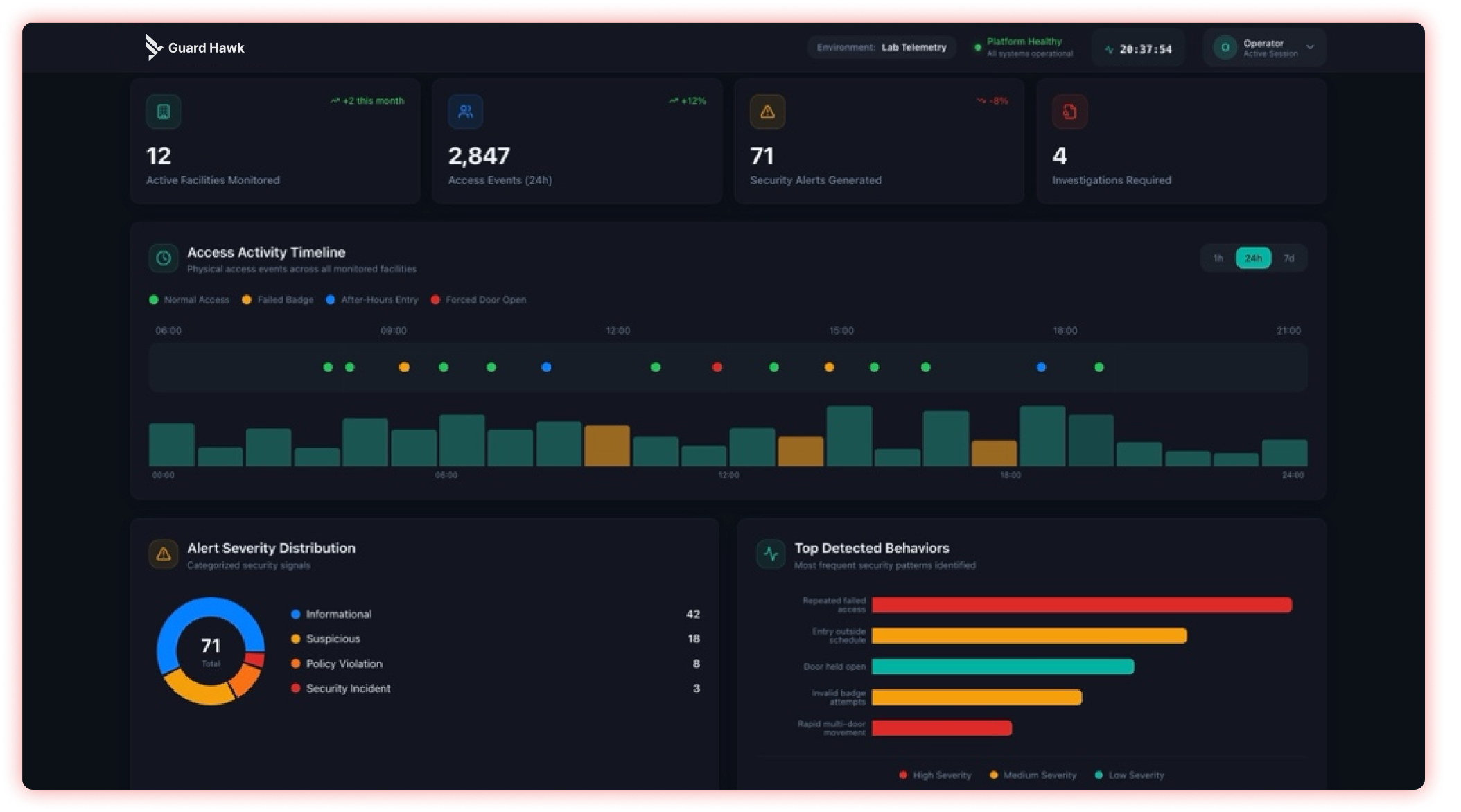
What Guard Hawk Detects in Real Time
Unauthorized Access Patterns
Detect correlated anomalies between badge activity, identity systems, and network behavior — not isolated access events.
Privilege Escalation Risks
Identify when elevated access across physical and digital systems introduces risk to critical infrastructure.
System & Controller Failures
Detect communication loss, configuration drift, and system disruptions across access control and infrastructure before they create blind spots.
Cross-System Behavioral Anomalies
Correlate access logs, identity activity, and infrastructure signals to uncover hidden threat patterns across environments.

Data Exfiltration Risk
Detect when sensitive data movement aligns with unusual access patterns, privilege changes, or physical presence anomalies.
Core Value
One Platform. Real-World Threat Visibility.
A unified detection platform connecting physical security systems and IT infrastructure.
01
Detect
Identify anomalies across access control, identity systems, and infrastructure — before they escalate into incidents.
02
Correlate
Connect events across physical and digital systems to reveal context — not isolated alerts, but actionable intelligence.
03
Respond
Act quickly with prioritized, high-confidence alerts tied to real-world activity across your environment.
Use Cases
Built for Real Security Environments
Detection scenarios across the physical security systems your organization already runs — no rip-and-replace required.
Access Control
Access Control Threat Detection
Genetec / LenelS2
Detect unauthorized access attempts, role changes, and system failures — correlating events across doors, controllers, and identity systems.
Video Surveillance
NVR / DVR Monitoring
IP Cameras · Network Video Recorders
Identify recording gaps, configuration issues, and connectivity failures across video surveillance systems before visibility is lost.
Identity Systems
Privilege & Identity Monitoring
HID · Active Directory
Detect identity misuse, credential anomalies, and privilege escalation tied to physical access events.
Network Infrastructure
Infrastructure Anomaly Detection
Firewalls · Switches · Appliances
Surface communication failures, configuration drift, and abnormal system behavior across network and security infrastructure.
Services Overview
Threat Detection + System Integrity. Unified.
Threat Detection
Detection across systems
Alerting + correlation
Continuous monitoring
System Monitoring
System integrity
Configuration drift
Operational risk visibility
Product Spotlight
Guard Hawk Talon
Learn More
Deploy rapidly without replacing your existing systems. Guard Hawk Talon enables secure telemetry collection and integration across environments — delivering visibility in hours, not months.
Why Guard Hawk
Why Organizations Choose Guard Hawk
Veteran-Owned
Built with operational discipline and mission focus
Vendor-Neutral
No proprietary lock-in — works across your existing stack
Detection Intelligence
Purpose-built detection logic for real-world signals
Built for Real Environments
Industrial, logistics, and commercial infrastructure

Proven Security Experience
Built on over a decade of combined cybersecurity and physical security expertise across real-world environments.
Detection Validation
Detection You Can Trust
Every detection scenario is tested and validated through structured detection validation records — ensuring alerts are accurate, reliable, and actionable.
Get Started
See What Your Security Stack Is Missing
Experience how unified detection reveals threats other systems miss.
